For admins
The Debricked GitHub app has two main configurations:
-
connecting to all repositories in your organization
-
connecting only to one or more selected repositories
Configure all of your repositories
-
Push a commit to the repository you want to connect
-
That's it! Commits are automatically picked up and scanned by the Debricked GitHub app.
As the scan is completed, results will be available in the GitHub check for the commit and in the Debricked UI - and all future pushes will be scanned automatically.
Configure selected repositories
-
In GitHub, go to Settings
-
Click on Applications
-
Choose Configure Debricked
-
Select the repositories you want to connect from the dropdown
-
Click Save
-
Push a commit to the now connected repository
-
Commits will now be automatically picked up and scanned by the Debricked GitHub app
As the scan is completed, results will be available in the GitHub check for the commit and in the Debricked UI - and all future pushes will be scanned automatically.
For users
To integrate Debricked via the GitHub App:
-
Visit our website
-
Click on Login with GitHub
-
Grant Debricked the right to SSO login
-
Select your company's organization
-
Input your email address
-
Enter your name and complete the sign-up process
GitHub Checks
You’ll be able to see the scan results and progress in the GitHub check. You can find it by clicking the symbol next to the commit hash.
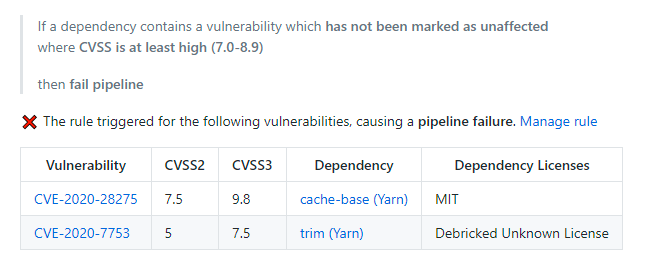
The contents of the GitHub Check are:
-
The amount of vulnerabilities found in the repository
-
Which automation rules were checked
-
Which automation rules were triggered
-
What triggered the automation rules
-
suggested fixes and fix Pull Requests
Here’s an example of a rule that fails the GitHub check:
There are three main types of automation rules
-
Rules that fail the GitHub Check
-
Rules that throw a warning in the GitHub Check
-
Rules that do not affect the GitHub check (e.g. rules sending an email)
Debricked UI
The Debricked tool contains everything you need to know about your dependencies and their vulnerabilities, e.g. detailed descriptions, automation rules, high risk licences, and more.
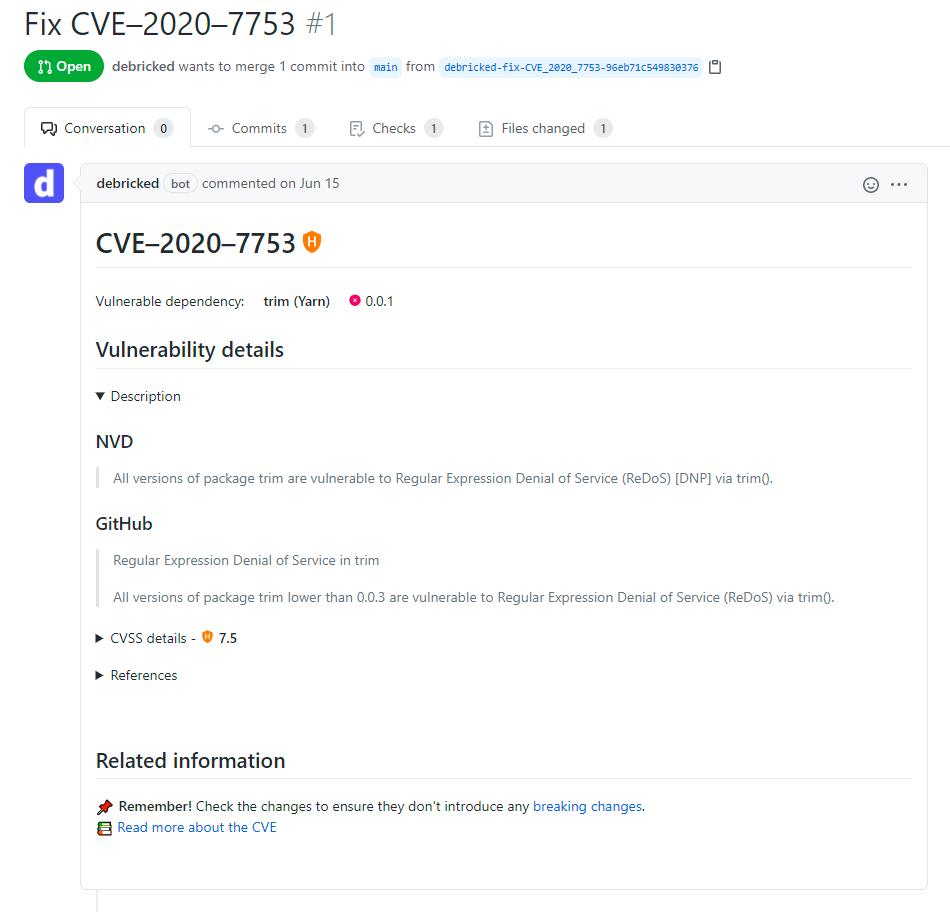
Pull Requests (PRs)
Opened PR contains useful details about the vulnerability it fixes, their severity and links to other resources.
Emails
Don't want to check the GitHub checks? Get emails showing you exactly what trigged a rule.
How to make the checks pass?
What is required to make a check pass is dependent on the rule that failed. Based on the rule you may need to fix or review a vulnerability or remove a dependency altogether incase of a license violation.
Fix vulnerabilities using Pull Requests
There are two types of Pull Requests openened by Debricked.
-
Lock file-fixes - work by updating indirect dependencies (dependencies of dependencies) within the version range as specified by their parent dependency. This minimizes the risk of breaking changes, but doesn't cover all cases
-
Deep fixes - work by figuring out which version of the direct dependency (the one you imported) contains a safe version of the vulnerable indirect dependency. This is useful in cases where the fixed version is outside of the allowed version range, as it's not possible to update the indirect dependency directly in those cases
To open a PR:
-
Navigate to the repository in the Debricked UI
-
Click on Open PR and select a target branch
-
Click Confirm
-
Run the changes through your tests and merge
-
This opens a PR with all possible lock file fixes and often allows you to fix a large chunk of your vulnerabilities in one PR
-
Go back to the repository
-
Go into each vulnerability and click Open PR from there
-
Click Confirm
This opens deep fixes for the vulnerabilities that were not solved by the lock file fix. Make sure to properly test the changes, as there's a risk of breaking changes due to possibly large version jumps required to fix vulnerabilities.
